NAC has a reputation: complex to deploy, expensive to maintain, and held together by 802.1X infrastructure that takes months to build and breaks the moment a device doesn’t support it. That reputation is not wrong. It describes what happens when NAC is implemented the way it was sold in 2008.
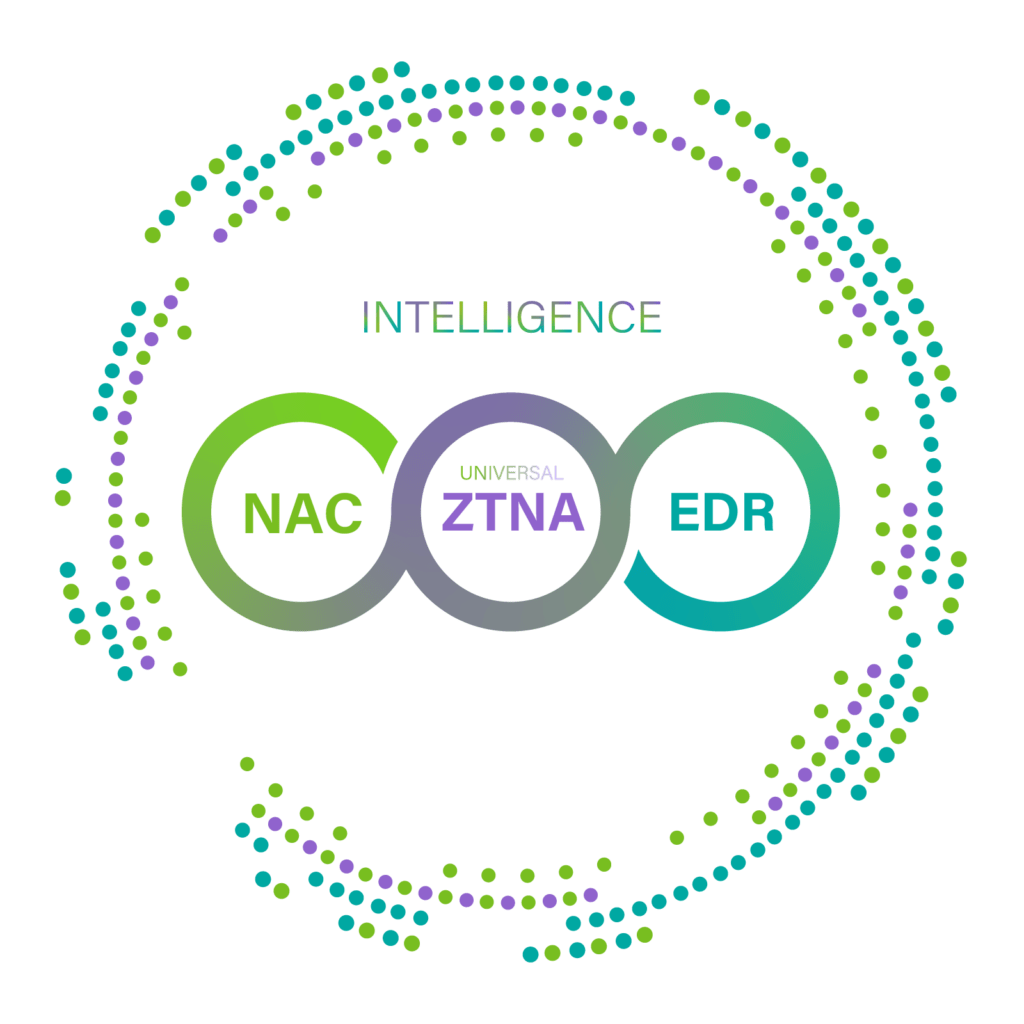
In 2026, networks include managed endpoints, IoT sensors, OT equipment, medical devices, building controllers, personal mobile hotspots, and SaaS-connected BYOD — on the same infrastructure. 802.1X does not reach most of this. Firewalls and SIEMs detect threats above Layer 2 but cannot isolate a device within its own segment. Shadow IT persists not because employees ignore policy, but because IT says no without offering an alternative.
This series covers NAC as it actually operates in 2026 — from the first packet at the connection point to the exception engine that keeps modern networks running. Eleven videos, four groups, one platform.
Which video should you watch first?
Pick your role. Start there. Watch in any order after.
- The Connection Point Is the Attack Surface
- NAC Enforcement: Why Projects Stall
- 7 NAC Enforcement Methods
- NAC Enforcement by Industry
- Genian NAC Editions & Licensing
- NAC as a Service 2026
- NAC Pricing
- Running NAC with Cisco, Palo Alto, FireEye, Infoblox
- Most NAC Agents Stop at Compliance
- Shadow IT
- The NAC Practice That Actually Pays
NAC Fundamentals
1. The Connection Point Is the Attack Surface: IP, MAC, Switch Port, SSID
What you’ll learn: Why every security incident starts at Layer 2 — before the firewall sees anything.
Every device that connects to a network — managed endpoint, IoT sensor, personal laptop, rogue access point — registers a MAC address, receives an IP, and binds to a switch port or SSID. That binding is the attack surface. Eight network access indicators determine whether that device can be identified, classified, and controlled. This video covers what those indicators are and why the connection point is where security either starts or fails.
2. NAC Enforcement: Why Projects Stall Before a Single Policy Applies
What you’ll learn: The five points where NAC deployments stop — and how each one is structural, not technical.
3. 7 NAC Enforcement Methods: Which One Fits Your Network
What you’ll learn: ARP, SPAN, 802.1X, DHCP, SNMP, inline, agent — what each requires and where each applies.
4. NAC Enforcement by Industry: BFSI, Healthcare, Manufacturing, Government
What you’ll learn: How enforcement configuration differs when your network includes ATMs, infusion pumps, PLCs, or classified systems.
Platform, Deployment & Cost
5. Genian NAC: Editions, Deployment, and How It Compares to Cisco ISE, ClearPass, FortiNAC, and Forescout
What you’ll learn: Licensing structure, upgrade risk, and what each platform actually costs to operate — from official vendor documentation.
6. NAC as a Service 2026: Start with a Subscription
What you’ll learn: How MSP/MSSP partners deliver NAC without a policy server per customer — and what that means for margin.
7. Network Access Control (NAC) Pricing: Why Is It So Hard to Get a Straight Answer?
What you’ll learn: Why NAC pricing is deliberately opaque — and what the real cost structure looks like across Cisco ISE, ClearPass, FortiNAC, Forescout, and Genian NAC.
NAC vendors do not publish list prices. Cisco ISE pricing depends on license tier (Essentials, Advantage, Premier), node count, and whether posture, pxGrid, or RADIUS proxy modules are required. ClearPass requires separate OnGuard licenses for endpoint compliance. FortiNAC compliance functionality requires FortiClient EMS — a separate server and license. Forescout eyeExtend Connect modules are term licenses priced per integration. This video covers why NAC pricing is structured to be difficult to compare, what the real total cost of each platform looks like when all required components are included, and how Genian NAC’s edition structure differs.
Integration & Agent
8. Running NAC with Cisco, Palo Alto, FireEye, and Infoblox: Who Actually Stops the Threat at Layer 2?
What you’ll learn: What happens after your SIEM generates an alert — and why the device is still connected.
9. Most NAC Agents Stop at Compliance. This One Doesn’t.
What you’ll learn: USB control, screen lock, wireless SSID policy, Windows Update — what Genian NAC includes that competitors sell separately.
Real-World Challenges & Partners
10. Shadow IT: If Blocking Isn’t the Answer, What Is?
What you’ll learn: Why every security incident starts at Layer 2 — before the firewall sees anything.11. The NAC Practice That Actually Pays: A Partner Guide to Genians
What you’ll learn: How MSP, MSSP, reseller, and system integrator partners structure NAC — and where Genians Cloud-Managed NAC changes the project economics.
NAC projects that stall at Monitor Mode or fail during 802.1X rollout have a consistent pattern: the margin disappears in deployment complexity that was not scoped. This video covers the NAC practice model for MSP, MSSP, reseller, and system integrator partners — how to structure NAC as a service or project, where deployment complexity concentrates, and how Genians Cloud-Managed NAC changes the economics. Genians operates the policy server. The partner deploys sensors and manages policy. Adding a new customer does not require building new server infrastructure. BFSI customers with multiple financial institutions are managed under a single Cloud-Managed structure. The video covers how partners have structured this model across North America, Latin America, the Middle East, and Europe.